You’ve probably heard the word AES many times. You may have even asked yourself: what exactly is AES? What makes it special? If yes, then you’re in the right web spot as this blog will show you everything you should be aware of AES: Advanced Encryption Standard.
We can think of AES as an advanced block cipher that can support three key lengths: 128, 192 and 256-bit encryption. It offers excellent security over long term against brute force attacks.
As of the year 2022, AES was the most well-known encryption tool in the world. It’s employed for secure protocols to transfer files such as FTPS, HTTPS, SFTP, AS2, WebDAV, and OFTP. A majority of the VPN services utilize the highest degree that of AES encryption.
It is estimated that AES would be adopted to secure more than 50 percent of all data in the world. Sounds quite impressive, doesn’t it?
The governments of countries and large organizations over the globe authorize data transmission of classified & confidential information at the top secret level using AES.
History of AES
The older version of AES – Data Encryption Standard (DES) established in the late 1970s and finally accepted in 1977 was outdated and vulnerable to cyber-attacks as of the 1990s. Thus it was the US National Institute of Standards and Technology (NIST) made the decision to upgrade it using a more advanced standard.
Advanced version, popularly known as AES today, was made effective in May 2002. Other countries soon adopted the same system.
What Is AES?
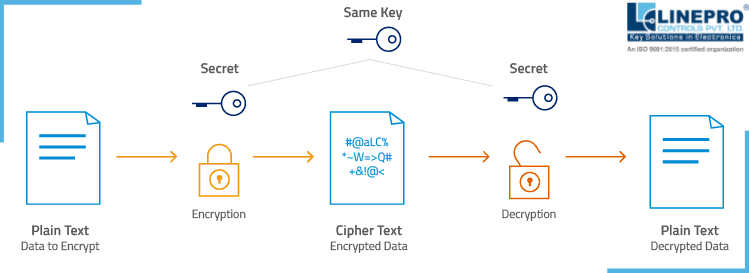
In its most basic form, AES is an algorithm for cryptography that is used to safeguard electronic information. It’s a symmetric block-cipher that is able to decrypt and encrypt information. Encryption transforms data into an unintelligible format called cipher text. The encryption process converts the data to its original form, which is known as plaintext.
Features of AES Encryption
- AES is a key encryption system that has a length of 128 bits, 256 bits or 192 bits. This key can be used to secure and decrypt data with 128 bits. It is the longest AES encryption keys length also referred to by the name of military-grade encryption. Although it’s the most secure, and the majority of the antivirus and password management solutions employ 256 bits, you’ll be comfortable using one of the two above mentioned options.
- It is also able to withstand almost all, if not all, certainly the known threats.
- Thirdly, it’s fast and compact across a broad variety of platforms. If you use the highest performance settings, you can reach 1.3 cycles per byte on a single core processor.
What if we don’t implement AES at all?
Cybercriminals, for instance, caused the world to lose around $6 trillion as of 2022, and they are predicted to triple to more than $18 trillion in 2025. The report reveals that cybercrime is more lucrative than the overall illicit drug trade and is the biggest transfer of wealth in the history of mankind.
The cybercrimes are on a steep rise as more and more devices are accessing wireless connections. Some devices like TVs, speakers and IoT devices employ sensors that collect and transmit data at unexpected levels.
Without AES encryption even something as basic as your keyboard, mouse or remote display could be a security flaw. This is not the only one of the most pressing security concerns that businesses have to face, especially IT & Software technology giants such as Microsoft acknowledge that the existing corporate encryption protocols used for passwords are seriously outdated. Certain security experts believe that the necessity to regularly change passwords is more of a security risk than it is a way to protect!
In a world ravaged by cyber-attacks, AES encryption gives businesses the tools needed to stay secure.
Working of AES
Like other ciphers, AES utilizes rounds of encryption to execute the transformations of ciphers. Each round usually consists of several blocks that are designed in a way to produce an operation, which can be repeated multiple times. The amount of rounds AES does is proportional to the length of the key.
In contrast to its predecessor, the previously mentioned DES which could only secure half the data path per cycle, AES is capable of encryption of the entire data path in a single round.
Each round is comprised of 4 layers.
1. SubBytes: SubBytes provides excellent confusion. “Confusion” is a term related to AES, is a characteristic of the operation of a secure encryption. It makes the relation between the ciphertext as well as the symmetric key as complicated as is possible. This leads to non-linear tables which are very effective in getting rid of patterns.
2. ShiftRows: ShiftRows provides diffusion – “diffusion” is another property of of an AES encryption. The objective here is to spread the structure of plaintext across the ciphertext, spreading each portion of the input to each part of output.
3. MixColumns: MixColoumns provides further diffusion to increase the efficiency.
4. AddRoundKey: AddRoundKey mixes the key and the cipher, making it difficult for a cyber-attacker to figure out the purpose of the cipher.
Incredibly, the last round is not equipped with the MixColumns layer. This means that this encryption algorithm secure.
The introduction of a subkey at the beginning and close is called key whitening.
Implementation of AES
The creators of the AES algorithm made clear in their initial plan that none of its algorithms could be patented. This is why it is completely free to use. It can be found in any kind of firmware, software hardware, and any combination of the two. The most frequent use you’ll find is…
Security protocols for Wi-Fi, for example WPA-PSK (AES) and WPA2-PSK (AES). There is a tendency to find the recent TKIP (Temporal Key Integrity Protocol) along with AES. The initial purpose behind TKIP is to substitute for the insecure WEP (Wired Equivalent Privacy). It didn’t provide much improvement over WEP’s predecessor. Therefore, the more secure AES came with the brand new WPA2 (Wi-Fi Secured Access II) encryption method.
The security strength of encryption is based upon the numeric key length which scrambles and decrypts messages.
It’s impossible to successfully carry out a brute force attack against AES-256. Any attempt to do so would require approximately the same number of combinations as 1,100 and then 75 zeroes. Quite discouraging for a cyber-criminal for trial and error procedures!
However, keep in mind that, in order to crack AES structure you’ll need to be closer, say within radius of 3 feet from whatever device you’re trying to target.
What is the significance of AES encryption in today’s world?
At the time of writing this blog, AES remains the most commonly used encryption software to safeguard digital data across the globe. In addition, it’s likely to remain this way for at least the foreseeable future.
You’re probably using it on the device you’re using to read this article!
In which country is AES encryption employed?
It is used in a myriad of firmware, software and hardware devices, or in any combination of these. The most popular use for it is in Wi-Fi, specifically WPA2-PSK (AES). It is also possible to also use it in various programming languages like Crypto++, Java and Python as well as within Facebook Messenger!
How secure is AES?
It’s very secure! Its biggest key length (256-bit) can withstand any attempt to brute force. It was only in the year 2017 when Dutch researchers were able to obtain encryption keys using an attack, using a side channel made possible by an improved antennas as well as signal processing.
Are AES accessible for free?
It is accessible to everyone. The founding fathers stated that it wouldn’t be the subject of patents.
What if there is no AES Encryption?
As per industry experts, the cyber-attacks cost globally about $6 trillion and will cost about $9 trillion by 2025. It is evident by comparing with illegal drug trade that cyber-attacks score more in terms of annual turnover. Rather, Cybercrime is most profitable in terms of greatest transfers in history.
Products incorporating AES encryption

Linepro is designer, developer and manufacturer of customized input devices, with added feature of AES encryption for metal keyboards & keypads, membrane keyboards & keypads and capacitive touch sense panels. The above image is a 52 key flat key metal keyboard with AES encryption. When input is registered on any key, data is transferred in encrypted format through the USB which is decrypted at the user’s end.
At Linepro, we understand the cyber security concerns of governments and organizations that is the reason we deliver hi-tech security for our input devices in form of AES. We can design customized input devices with AES encryption depending on the need of the security strength. Please share your requirements with us, and our consulting team shall guide you the best!

